Detailed control
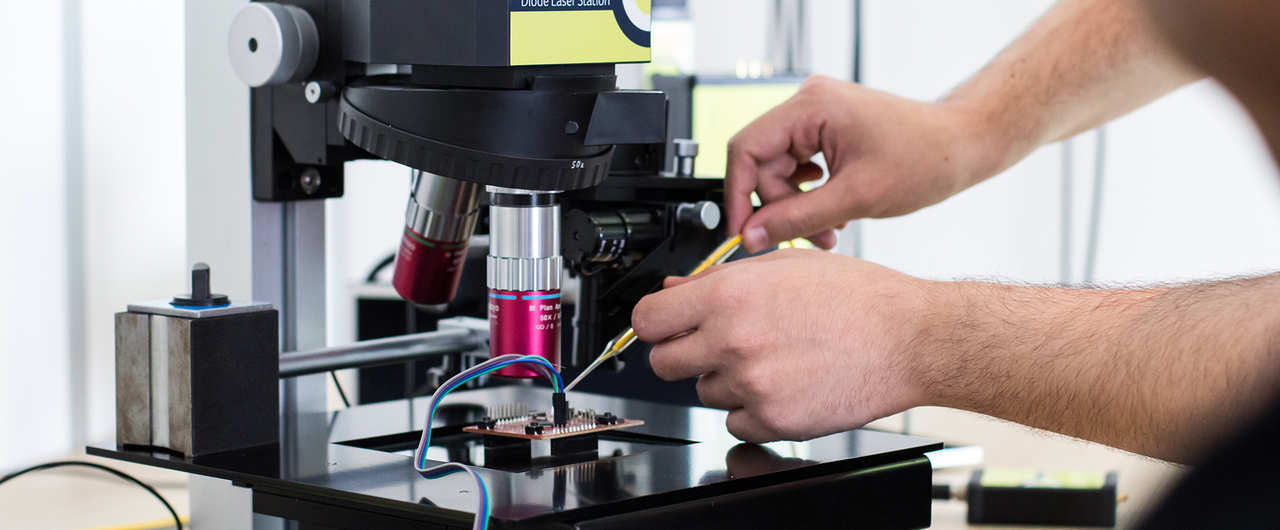
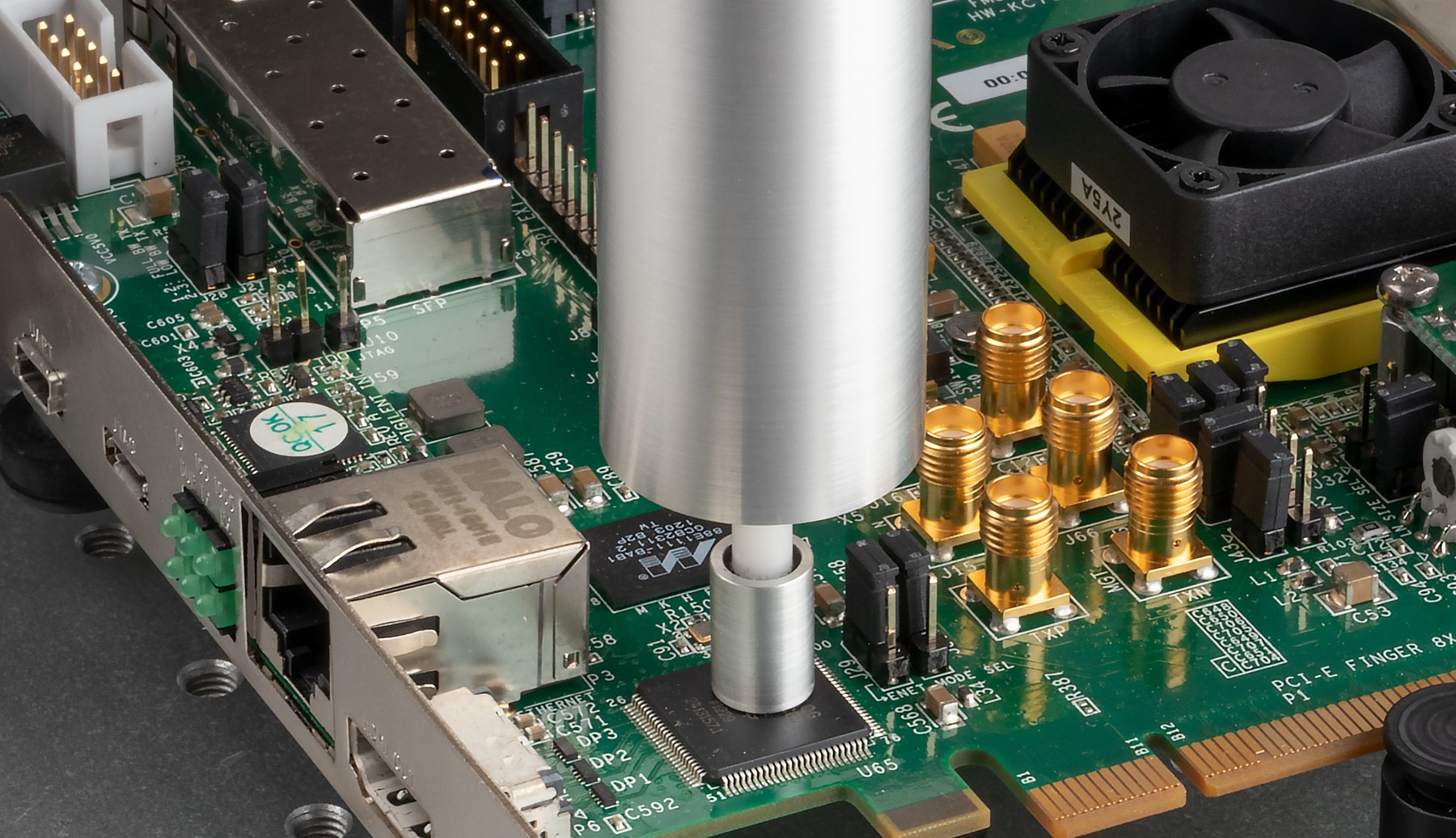
Inspector FI – Fault Injection – offers all features to perform fault injection testing on embedded systems and smart card technology. Our hardware components cover accurate, reliable and thus predictable, clock and voltage glitching, and advanced optical attacks with purpose-built laser equipment. Fault injection attacks – also known as perturbation attacks – change the normal behaviour of a chip by inducing an exploitable fault. With Inspector FI, a user can test if a key can be extracted by inducing faults in a chip’s cryptographic operations, bypass a check such as an authentication or a lifecycle state, or change the program flow of code on the chip.
Worldwide standard
Used by organisations worldwide, the integrated modular platform of Inspector combines analysis and fault injection test modules. Pushing the boundaries for off-the-shelf Fault Injection testing hardware, Riscure Inspector is valued by analysts for the flexibility and top end specifications. Custom designed hardware and software enable government institutions, security evaluation laboratories and chip manufacturers around the globe to perform time efficient, reproducible, cutting edge security research.
Key features
The all-in-one security solution for detailed control over the entire side channel testing process.
Hardware
Optimized for outstanding FI results, our hardware is designed with the requirements of the user and business in mind without losing flexibility. Ease of use, effortless configuration and seamless integration with Inspector SCA software or extend your own platform using the SDK on selected devices. The entire portfolio of Riscure Security Testing Solutions and complete tool sets is available in our automated quotation system.
Learn more about Riscure Training Academy
Basic and advanced courses on Fault Injection to help you fine-tune Inspector to suit your needs.
Support
Software updates
Riscure Inspector is regularly updated to improve side channel and fault injection testing efficiency, user experience and introduce fixes. New software releases are available free of charge to customers who purchased one of our Subscription Packages.
Check the latest release notes for Inspector SCA and FI here.
Updates on new developments
The world keeps moving: every year new attacks and methods are introduced. To keep you up-to-date we select practical attacks and make these available to our users.
For optimal performance of the software read the latest specifications of the PC workstation that we supply.
Support Portal
Tutorials, manuals, FAQ, release notes, software updates, issue tracking and much more can be found on our support portal. Please sign up and login at: https://support.riscure.com/
An annual user workshop
We organize two-day user workshop where we will present the latest developments in side channel analysis and fault injection testing and provide practical tips. The User Workshop is free of charge to Riscure Inspector subscribers or legacy Support Contract holders.
Dedicated support
We have a full-time support team to help with any issues you might face while doing your work. Our skilled people will try to get you back on track as fast as possible.
For technical assistance call +31 (0) 15251 4090 or visit our support portal
Riscure Inspector subscription
Riscure Inspector is available via the annual software subscription. We deliver Inspector to organisations in line with our Inspector Sales Policy. During the duration of subscription, the Riscure Inspector is kept up-to-date and users are invited to the annual Inspector User Workshop.
Sales policy

- Contact us
-
Bartek Gedrojc 大虎
- Sales and Business Development Director Tools