Watch the video of this research presented at SHA2017:
Why is it so hard to make secure chips?
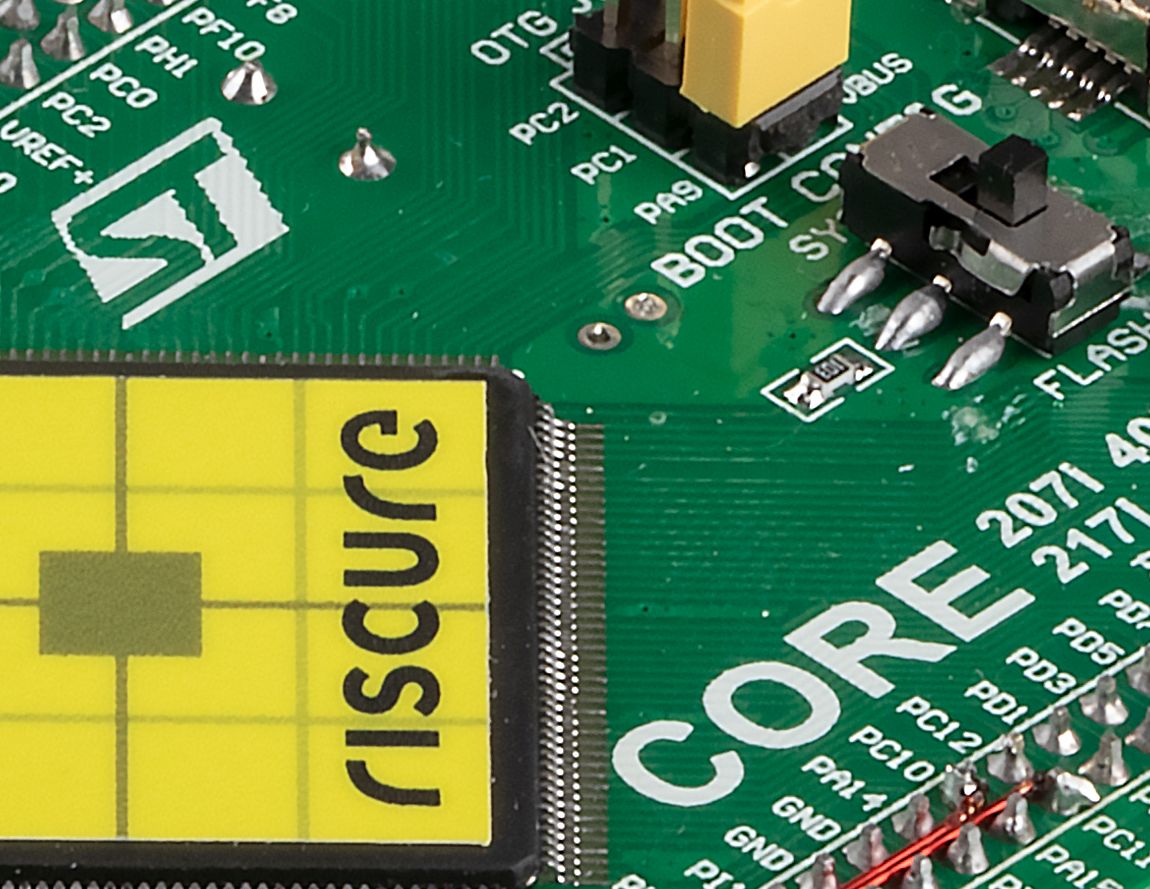
Why is it so hard to make secure chips? from Riscure
Watch the video of this research presented at SHA2017
Watch the video of this research presented at SHA2017:
Why is it so hard to make secure chips? from Riscure
Typical threat modeling applied in cryptography involves a malicious third party attempting to access content. Download the whitepaper.
Side-channel attacks are techniques to attack implementations of cryptographic algorithms by observing its physical parameter. Read more.