Watch the video of this research presented at SHA2017:
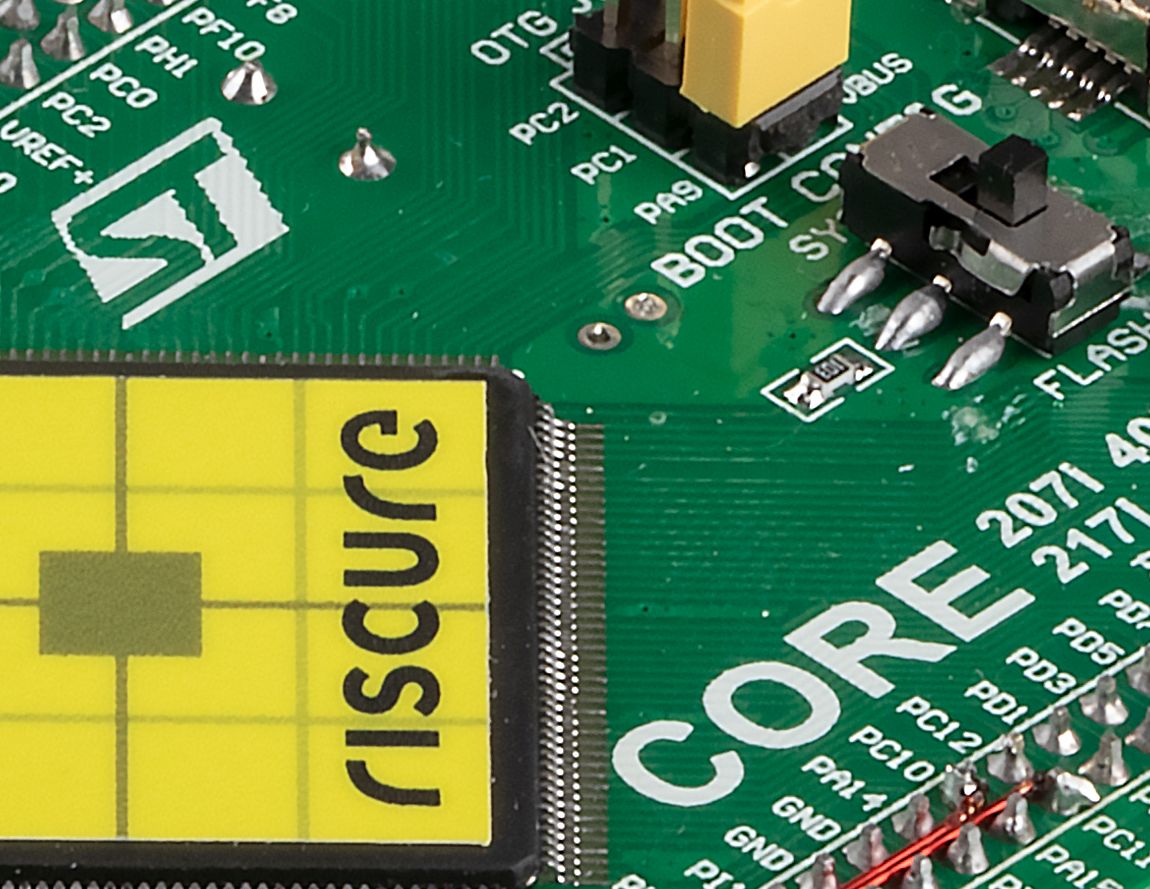
Practical steps to evaluate and protect Secure Boot
This paper reveals common weaknesses in Secure Boot implementations and proposes practical steps to enhance security of this critical element of an embedded system.