ARM based, fast and feature rich SOC
Fault injection attacks are a powerful technique to influence the intended behavior of embedded systems. They can be used to exploit or bypass robust security features found in secure embedded systems. Examples of such attacks include differential fault analysis (DFA) and bypassing authentication mechanisms. An embedded system’s authenticated boot chain (i.e. secure boot) is an interesting target for fault injection. The initial boot stages are of limited size which means logically exploitable vulnerabilities are not guaranteed to be present. In this paper, we introduce an ARM specific fault injection attack strategy for exploiting embedded systems where externally controlled data is loaded in the program counter (PC) register of the processor. This allows an attacker to control the target’s execution flow which eventually will lead to arbitrary code execution on the target. We first simulate the attack using a common fault model, after which we demonstrate the practicality of the attack using a development platform designed around an ARM based, fast and feature rich system on chip (SOC). We conclude with an overview of effective and non-effective countermeasures against this fault injection attack technique.
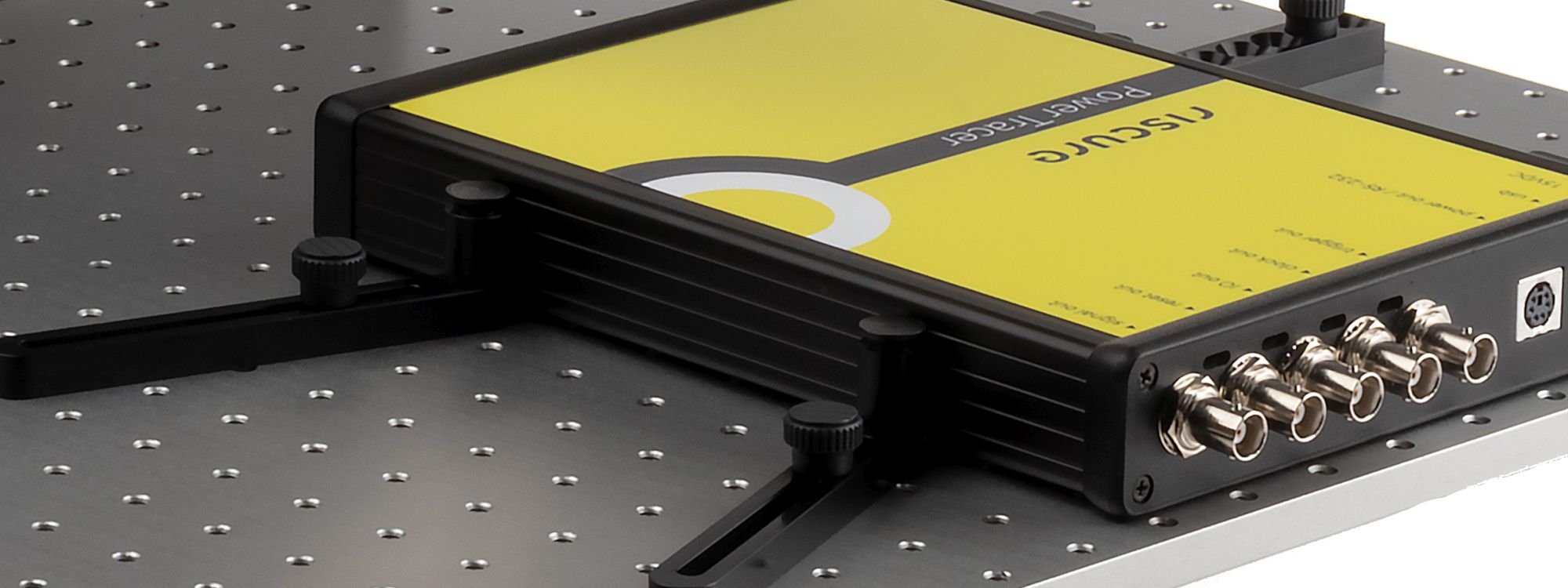
The slides from the original presentation at FDTC (download pdf):