Threat modeling in cryptography
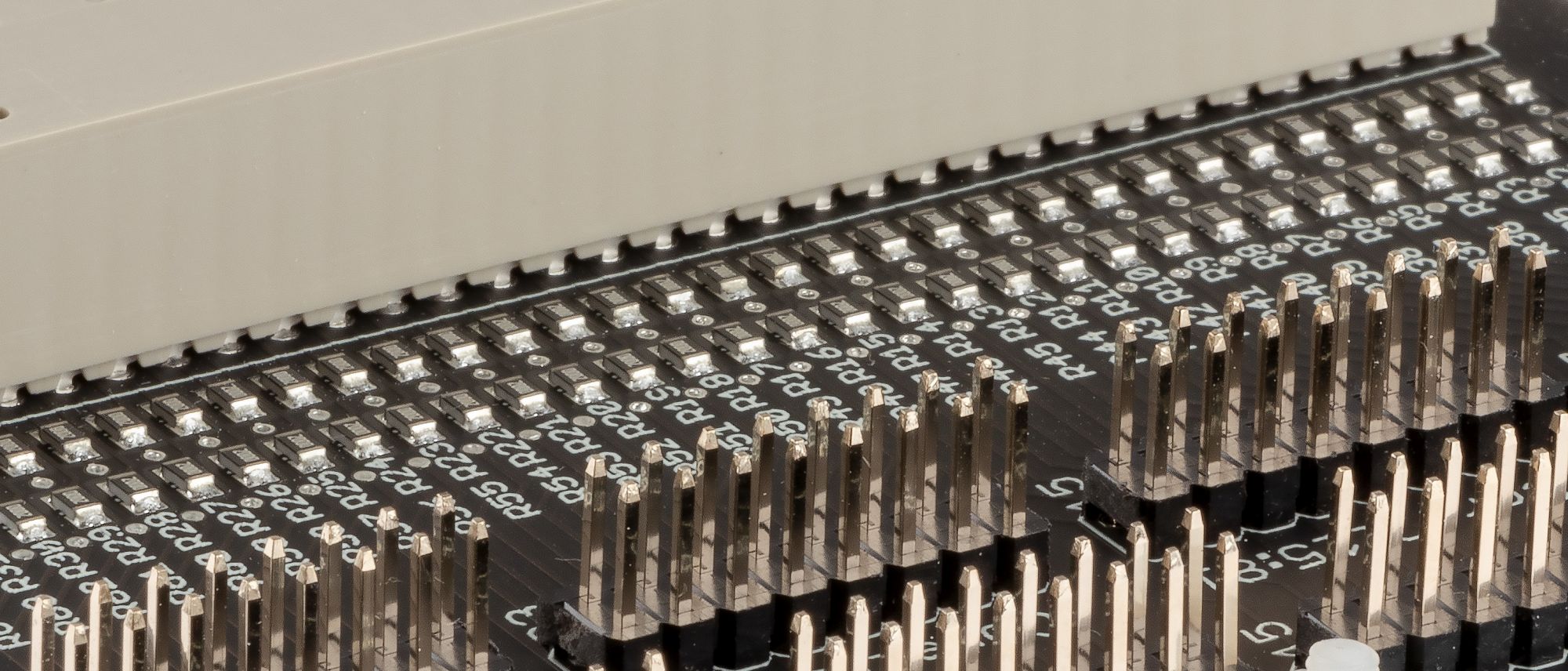
Typical threat modeling applied in cryptography involves a malicious third party attempting to access either the keys used for protecting the content or the protected content itself. In this model, which we refer as the “Black-Box” model, the attacker is assumed to be able to observe and alter the ciphertext, without having access to the systems performing cryptographic operations.
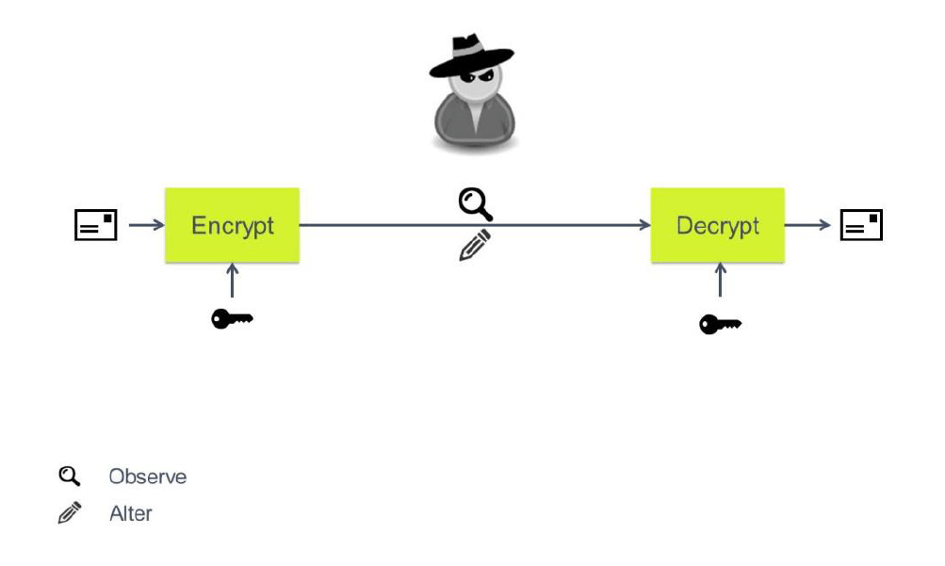
“Gray-Box” model
In some cases the threat model is augmented with the attacker’s ability to interact with the systems performing the crypto operation, via observation and/or alteration of system parts and processes. We refer to this model as “Gray-Box” model, where the attacker has access to the system, but he is still not allowed to access the key and/or to tamper with the cryptographic algorithm and its implementation.
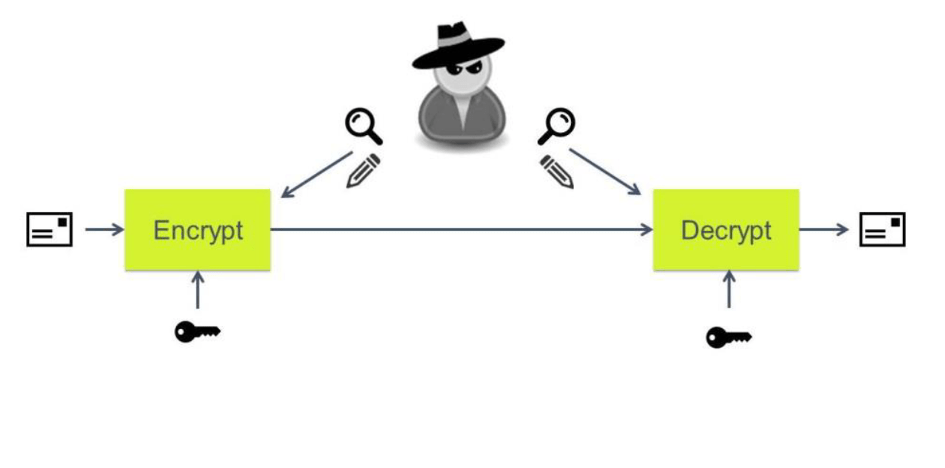
“White-Box” model
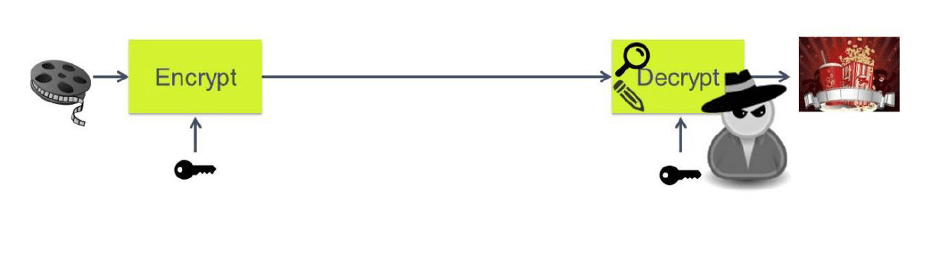
Both models rely on having two friendly parties communicating, while the attacker is none of the parties. In the described scenario,
instead, the attacker can be one of the communicating parties, which must have limited and controlled access to the provided goods or service. This explains the need for a different threat model which we will refer to as “White-Box” model.
In the White-Box threat model:
• The attacker can observe the encryption process from within the system
• The attacker can modify anything at will, including the cryptographic algorithm
Achieving security within this model is very difficult, as the cryptographic keys used for protection are stored in the system and potentially available to the attacker. Protecting such keys becomes the fundamental security challenge and this is what white-box cryptography tries to achieve.