Advisory by Espressif Systems is available here.
The pitfalls of hardware security
Securing IoT solutions increasingly becomes an essential practice, for a number of reasons. It allows to protect a vendor’s intellectual property by encrypting the firmware. It reduces impact on customers, who, in the event of a remotely exploitable vulnerability, risk losing sensitive data. In other cases IoT becomes a point of entry to access business and consumer local networks.
The security industry is primarily focused on finding and mitigating vulnerabilities in software, while the robustness of hardware is often overlooked. We have previously shown how attacks on hardware can help extract secrets. Notable IoT implementations often lack basic security measures which allows effortless analysis of firmware for further exploitation.
Even if IoT firmware is properly protected, a vulnerable implementation of Secure Boot may render other security mechanisms useless. In some cases, secure initialization of a device can be circumvented by a power glitch. This is exactly what happened with ESP32.
The vulnerability
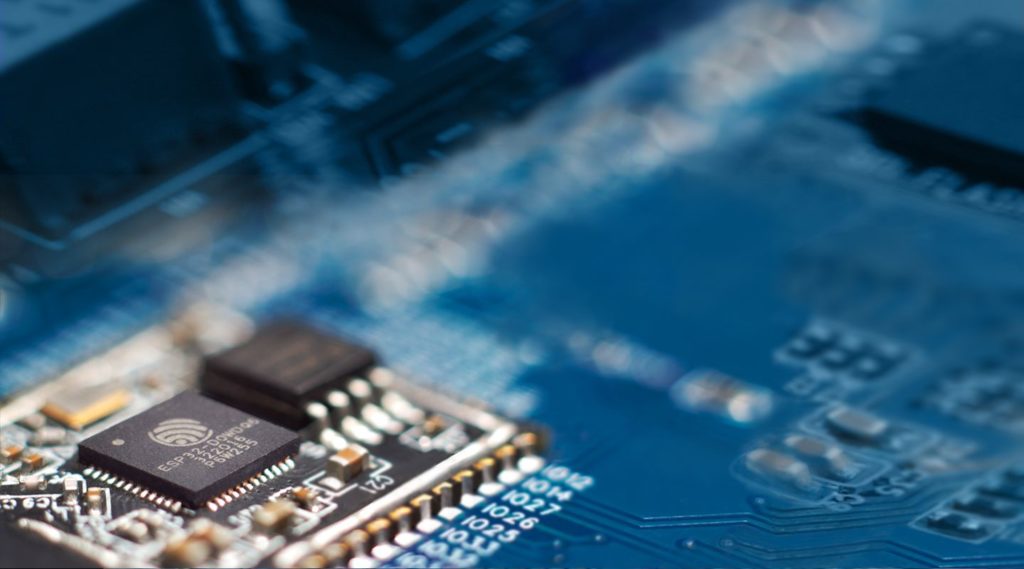
The problem was discovered by Riscure researchers Yashin Mehaboobe and Santiago Cordoba Pellicer in April 2019. An analysis of the ESP32 chip using Riscure Inspector solution revealed a set of parameters (such as voltage and timing) that allowed to bypass the Secure Boot verification mechanisms and, ultimately, execute unverified code stored on flash. The issue could be mitigated by enabling a built-in Flash Encryption feature of ESP32. Espressif Systems also plans to release the updated revision of an SoC with further improvements to harden against Fault Injection attacks.
As an expert in Side Channel Analysis and Fault Injection techniques, Riscure can help you make your device robust against increasingly affordable and widespread hardware attacks. We specialize in security of embedded and connected devices, including Smart Cards and IoT. To learn how we can help you achieve better security in your development process, feel free to get in touch with us via inforequest@riscure.com.